kryptos
Can you see anything Q?
— K3 excerpt
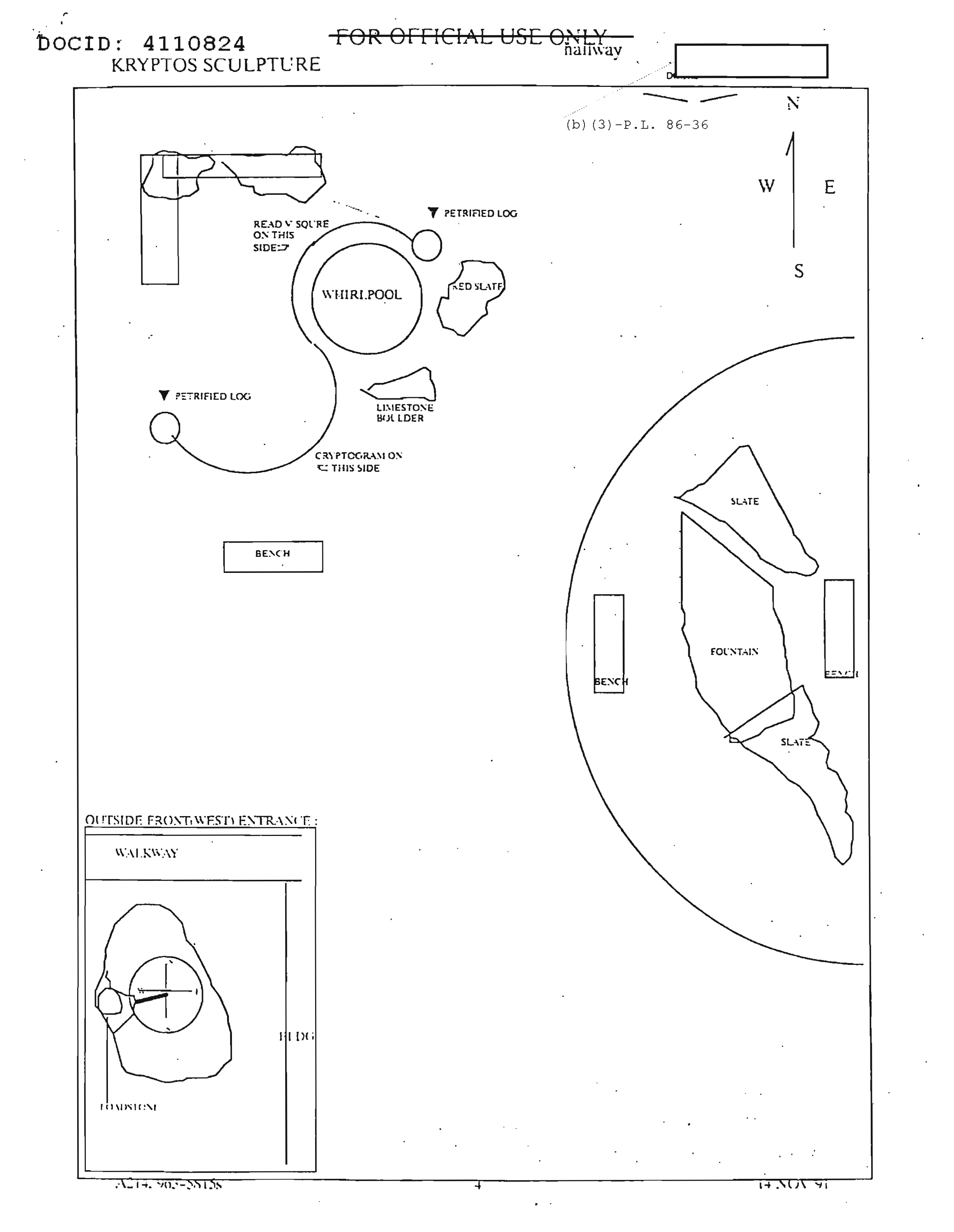
Kryptos is a sculpture made by Jim Sanborn. It’s located in the CIA headquarters in Langley, Virgina. The name comes from the ancient Greek κρυπτός which means hidden
.
EMUFPHZLRFAXYUSDJKZLDKRNSHGNFIVJ | ABCDEFGHIJKLMNOPQRSTUVWXYZABCD |
ENDYAHROHNLSRHEOCPTEOIBIDYSHNAIA | NGHIJLMNQUVWXZKRYPTOSABCDEFGHIJL |
Kryptos features four blocks of text on a scroll-shaped copper sculpture. The left column contains the cipher texts, and the right contains a keyed Vigenère encryption tableau. Morse code is also present. Starting from K0 (Morse code being the easiest to decode), each passage of Kryptos was intended to be solved sequentially.
K0
Detailed images of the Morse code can be found here.
Decoded, from Wikipedia:
E E VIRTUALLY E | E E E E E E INVISIBLE
DIGETAL E E E | INTERPRETATIT
E E SHADOW E E | FORCES E E E E E
LUCID E E E | MEMORY E
T IS YOUR | POSITION E
SOS
RQAlthough I’m not sure if the above is accurate. DOCID 4050955 from the declassified NSA documents has a slightly different transcript. The direction of the Morse code is also not discernible, so they also considered reading it backwards. I’ve highlighted some palindromes throughout the code that I found interesting:
. . . ..-. -. - .. .-- .. ..-
E E E F N T I W I U →
E E E L A T I G I D ← DIGITAL
- .. - -. - . .-. .--. .-. . - .- ..
T I T N T E R P R E T A I →
T I T A T E R P R E T N I ← INTERPRET (AT?) (IT?)
T I T A T E R P R E T N I
.-. -.. --- --.- ... .. -
R D O Q S I T →
R U O Y S I T ← T IS YOUR
. .- --- .. - .. ... --- .--.
E A O I T I S O P →
E N O I T I S O P ← POSITION
... --- ...
S O S ←/→
. --.- ..-. ..-. -. -.. - .-. .. -... . .
E Q F F N D T R I B E E →
E Y L L A U T R I V E E ← VIRTUALLY
. ..-. ...- .. ... .. -... .- .. . . . . .
E F V I S I B A I E E E E E →
E L B I S I V N I E E E E E ← INVISIBLE
. . --. --- ..- -. .... ... . . .
E E G O U N H S E E E →
E E W O D A H S E E E ← SHADOW
. . . . . ... . .-.- .-. --- .-..
E E E E E S E ? R O L →
E E E E E S E C R O F ← FORCES
. . . ..- .. .-.- -.. ..-.
E E E U I ? D F →
E E E D I C U L ← LUCID
. --.- .-. --- -- . --
E Q R O M E M →
E Y R O M E M ← MEMORY
-.-- .-.
Y R →
Q R ←DIGITAL EEE
INTERPRETATIT
TISYOURPOSITION E
SOS EE
VIRTUALLY EEEEEE
INVISIBLE EEE
SHADOW EE
FORCES EEEEE
LUCID EEE
MEMORY E
RQRegarding how K0 is supposed to have a clue for K1, it could just be a bias at this point, but you can kinda spell out "palimpsest" when you gather the middle letters of the palindromes:
IGI TIT TERPRET TAT ITI SOS ISI ESE MEM
G I P A T O S S E
_ I P A T _ S S E
P A _ I _ _ S E S TI could just be reaching though. It’s worth noting that the keywords for K2 and K3 were found using frequency analysis.
Notes:
- eeeee (5 dits) historically signified an error
- Unsure what to make of
INTERPRETATIT .-.-is either the prosign for new line (AA) or the procedure wordsALL AFTER
(AA)- Unsure what to make of
RQ, butQRQis a Q-code that meansShall I send faster?
K1
EMUFPHZLRFAXYUSDJKZLDKRNSHGNFIVJ
YQTQUXQBQVYUVLLTREVJYQTMKYRDMFDDecryption requires a keyword, which is PALIMPSEST in K1. Take the rows from the tableau that begin with the letters of the keyword and stack them beneath the Kryptos alphabet to form a new table.
Repeat the keyword along the cipher to get the letter pairs. The first cipher character is E and it corresponds to the keyword character P. Find E in the P row in the table. The resulting plaintext character B is where it aligns with in the top row.
EMUFPHZLRFAXY...
PALIMPSESTPAL...
BETWEENSUBTLE...
KRYPTOSABCDEFGHIJLMNQUVWXZ
PTOSABCDEFGHIJLMNQUVWXZKRY B
ABCDEFGHIJLMNQUVWXZKRYPTOS E
LMNQUVWXZKRYPTOSABCDEFGHIJ T
IJLMNQUVWXZKRYPTOSABCDEFGH W
MNQUVWXZKRYPTOSABCDEFGHIJL E
PTOSABCDEFGHIJLMNQUVWXZKRY E
SABCDEFGHIJLMNQUVWXZKRYPTO N
EFGHIJLMNQUVWXZKRYPTOSABCD S
SABCDEFGHIJLMNQUVWXZKRYPTO U
TOSABCDEFGHIJLMNQUVWXZKRYP B
...BETWEENSUBTLESHADINGANDTHEABSENC
EOFLIGHTLIESTHENUANCEOFIQLUSIONBETWEEN SUBTLE SHADING AND THE ABSENCE OF LIGHT LIES THE NUANCE OF IQLUSIONI’m not sure what clue is supposed to be in the plaintext that leads to K2's "abscissa," but you can certainly spell it out from it.
PALIMPSEST
BETWEENSUB
TLESHADING
ANDTHEABSE
NCEOFLIGHT
LIESTHENUA
NCEOFIQLUS
IONNotes:
- A palimpsest is
a manuscript page that has been reused for another document after erasing the original text
IQLUSIONis a deliberate misspelling
K2
VFPJUDEEHZWETZYVGWHKKQETGFQJNCE
GGWHKK?DQMCPFQZDQMMIAGPFXHQRLG
TIMVMZJANQLVKQEDAGDVFRPJUNGEUNA
QZGZLECGYUXUEENJTBJLBQCRTBJDFHRR
YIZETKZEMVDUFKSJHKFWHKUWQLSZFTI
HHDDDUVH?DWKBFUFPWNTDFIYCUQZERE
EVLDKFEZMOQQJLTTUGSYQPFEUNLAVIDX
FLGGTEZ?FKZBSFDQVGOGIPUFXHHDRKF
FHQNTGPUAECNUVPDJMQCLQUMUNEDFQ
ELZZVRRGKFFVOEEXBDMVPNFQXEZLGRE
DNQFMPNZGLFLPMRJQYALMGNUVPDXVKP
DQUMEBEDMHDAFMJGZNUPLGEWJLLAETGThe decryption process is the same as K1's, but this time with the keyword ABSCISSA.
VFPJUDEEHZW...
ABSCISSAABS...
ITWASTOTALL...
KRYPTOSABCDEFGHIJLMNQUVWXZ
ABCDEFGHIJLMNQUVWXZKRYPTOS I
BCDEFGHIJLMNQUVWXZKRYPTOSA T
SABCDEFGHIJLMNQUVWXZKRYPTO W
CDEFGHIJLMNQUVWXZKRYPTOSAB A
IJLMNQUVWXZKRYPTOSABCDEFGH S
SABCDEFGHIJLMNQUVWXZKRYPTO T
SABCDEFGHIJLMNQUVWXZKRYPTO O
ABCDEFGHIJLMNQUVWXZKRYPTOS T
...ITWASTOTALLYINVISIBLEHOWSTHATPO
SSIBLE?THEYUSEDTHEEARTHSMAGNET
ICFIELDXTHEINFORMATIONWASGATHER
EDANDTRANSMITTEDUNDERGRUUNDTOANU
NKNOWNLOCATIONXDOESLANGLEYKNOWA
BOUTTHIS?THEYSHOULDITSBURIEDOUT
THERESOMEWHEREXWHOKNOWSTHEEXACTL
OCATION?ONLYWWTHISWASHISLASTMES
SAGEXTHIRTYEIGHTDEGREESFIFTYSE
VENMINUTESSIXPOINTFIVESECONDSNO
RTHSEVENTYSEVENDEGREESEIGHTMINU
TESFORTYFOURSECONDSWESTIDBYROWSSomething to note here, K2 has an error. Sanborn omitted an S in the last line.
...GESWJLLAETGTherefore, rather than WESTIDBYROWS, it should be WESTXLAYERTWO.
The omission allowed the text to fit a 31-column grid perfectly:
VFPJUDEEHZWETZYVGWHKKQETGFQJNCE
GGWHKK?DQMCPFQZDQMMIAGPFXHQRLGT
IMVMZJANQLVKQEDAGDVFRPJUNGEUNAQ
ZGZLECGYUXUEENJTBJLBQCRTBJDFHRR
YIZETKZEMVDUFKSJHKFWHKUWQLSZFTI
HHDDDUVH?DWKBFUFPWNTDFIYCUQZERE
EVLDKFEZMOQQJLTTUGSYQPFEUNLAVID
XFLGGTEZ?FKZBSFDQVGOGIPUFXHHDRK
FFHQNTGPUAECNUVPDJMQCLQUMUNEDFQ
ELZZVRRGKFFVOEEXBDMVPNFQXEZLGRE
DNQFMPNZGLFLPMRJQYALMGNUVPDXVKP
DQUMEBEDMHDAFMJGZNUPLGESWJLLAETG
ITWASTOTALLYINVISIBLEHOWSTHATPO
SSIBLE?THEYUSEDTHEEARTHSMAGNETI
CFIELDXTHEINFORMATIONWASGATHERE
DANDTRANSMITTEDUNDERGRUUNDTOANU
NKNOWNLOCATIONXDOESLANGLEYKNOWA
BOUTTHIS?THEYSHOULDITSBURIEDOUT
THERESOMEWHEREXWHOKNOWSTHEEXACT
LOCATION?ONLYWWTHISWASHISLASTME
SSAGEXTHIRTYEIGHTDEGREESFIFTYSE
VENMINUTESSIXPOINTFIVESECONDSNO
RTHSEVENTYSEVENDEGREESEIGHTMINU
TESFORTYFOURSECONDSWESTXLAYERTWO
ITWASTOTALLYINVISIBLEHOWSTHATPO
SSIBLE?THEYUSEDTHEEARTHSMAGNETI
CFIELDXTHEINFORMATIONWASGATHERE
DANDTRANSMITTEDUNDERGRUUNDTOANU
NKNOWNLOCATIONXDOESLANGLEYKNOWA
BOUTTHIS?THEYSHOULDITSBURIEDOUT
THERESOMEWHEREXWHOKNOWSTHEEXACT
LOCATION?ONLYWWTHISWASHISLASTME
SSAGEXTHIRTYEIGHTDEGREESFIFTYSE
VENMINUTESSIXPOINTFIVESECONDSNO
RTHSEVENTYSEVENDEGREESEIGHTMINU
TESFORTYFOURSECONDSWESTIDBYROWSIT WAS TOTALLY INVISIBLE HOWS THAT POSSIBLE ?
THEY USED THE EARTHS MAGNETIC FIELD X
THE INFORMATION WAS GATHERED AND TRANSMITTED UNDERGRUUND TO AN UNKNOWN LOCATION X
DOES LANGLEY KNOW ABOUT THIS ?
THEY SHOULD ITS BURIED OUT THERE SOMEWHERE X
WHO KNOWS THE EXACT LOCATION ?
ONLY WW THIS WAS HIS LAST MESSAGE X
THIRTY EIGHT DEGREES FIFTY SEVEN MINUTES SIX POINT FIVE SECONDS NORTH SEVENTY SEVEN DEGREES EIGHT MINUTES FORTY FOUR SECONDS WEST X
LAYER TWOCould the numbers be spelling out something? I tried mapping those numbers to the Kryptos alphabet (x mod 26):
THIRTY EIGHT DEGREES 38 (E)
FIFTY SEVEN MINUTES 57 (T)
SIX POINT FIVE SECONDS 65 (F)
SEVENTY SEVEN DEGREES 77 (X)
EIGHT MINUTES 8 (A)
FORTY FOUR SECONDS 44 (L)
K R Y P T O S A B C D E F G H I J L M N Q U V W X Z
01 02 03 04 05 06 07 08 09 10 11 12 13 14 15 16 17 18 19 20 21 22 23 24 25 26
27 28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 49 50 51 52
53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78
ETFXAL
AXLEFT?ITWASTOTALLYINVISIBLEHOWSTHATPOSSIBLE
THEYUSEDTHEEARTHSMAGNETICFIELDXTHEINF
ORMATIONWASGATHEREDANDTRANSMITTEDUNDE
RGRUUNDTOANUNKNOWNLOCATIONXDOESLANGLE
YKNOWABOUTTHISTHEYSHOULDITSBURIEDOUTT
HERESOMEWHEREXWHOKNOWSTHEEXACTLOCATIO
NONLYWWTHISWASHISLASTMESSAGEXTHIRTYEI
GHTDEGREESFIFTYSEVENMINUTESSIXPOINTFI
VESECONDSNORTHSEVENTYSEVENDEGREESEIGH
TMINUTESFORTYFOURSECONDSWESTXLAYERTWO
LLPEATHIENDOLOKHUESWETTLEGFMPEHVEERSO
ABTHEETTHANTNDYTOIEXHAWSGISNXSTESTUEW
TIATENXATRUDWXETHRRETCWIAEEEIERSEUOWT
OSHEHGDMATDNONLUSUERSOYHSYEVSVOYENFSR
TITLTALRGDEUNOGOYBHEWLLSSTRESINTRIYDE
SVSBDMEOSNTUKINBESTHOTNAERGSEFSNGMTNY
ANWIESIFAATRNTAAHTTWNCOWMIEYTTDEETROA
WIOSSHFNWDIGUALWTIUEKANSTHDTUNNVDHOCL
TYHSUTCINEMRNCSOSDOMOXOISTTFNIOENGFEX
ILEOYRIEORSEAOENILDOHEIHAXHIIOCSEISSTTIWSHHMFETANIETOILNTYTOSEWCOWHEHHSVENCTYGHSUSY
OVOOTTSCHAGAMDDNTSKTEIDEROAIWSMTGEETIERTEGEODA
TNHP?DHITMSDSNNKAEYUHDERENXTYATXIESUOSONDITFNL
SIETEETTXRAENUUNCOEOTLIEHKEALWSEERYNPENENEUYOXO
AYLALSREDOWRADUUODLB?URHWOECNSAGYGTIXVSVESNTCTW
WLBHBUANLFNERERNLXGASOUTEHHOOILATEFMIIDEVEIREST
TLITIYEGENOHTTGANNNWIHBTMWTL?HSSRDINSFNSEEMOSER
IASSSEEAIIITDTROWOAOHSSUOXSTNTISITFESTOHSRTFRWETLITIUANLFNERERNLXGASURHWOECLWSEERYNPENENEUYOXO
IASSSYEGENOHTTGANNNWIOUTEHHONSAGYGTIXVSVESNTCTW
TIWSEEAIIITDTROWOAOHHBTMWTLOILATEFMIIDEVEIREST
OVOOHHMFETANIETOILNTSSUOXSTNHSSRDINSFNSEEMOSER
TNHPTTSCHAGAMDDNTSKTYTOSEWCOTISITFESTOHSRTFRWE
SIETEDHITMSDSNNKAEYUEIDEROAIWHEHHSVENCTYGHSUSY
AYLALETTXRAENUUNCOEOHDERENXTWSMTGEETIERTEGEODA
WLBHBSREDOWRADUUODLBTLIEHKEAYATXIESUOSONDITFNLTNHP?DHITMSDSNNKAEYUHDERENXTYATXIESUOSONDITFNL
SIETEETTXRAENUUNCOEOTLIEHKEALWSEERYNPENENEUYOXO
AYLALSREDOWRADUUODLB?URHWOECNSAGYGTIXVSVESNTCTW
WLBHBUANLFNERERNLXGASOUTEHHOOILATEFMIIDEVEIREST
TLITIYEGENOHTTGANNNWIHBTMWTL?HSSRDINSFNSEEMOSER
IASSSEEAIIITDTROWOAOHSSUOXSTNTISITFESTOHSRTFRWE
TIWSHHMFETANIETOILNTYTOSEWCOWHEHHSVENCTYGHSUSY
OVOOTTSCHAGAMDDNTSKTEIDEROAIWSMTGEETIERTEGEODANotes:
- The abscissa is the x-coordinate in a Cartesian plane
UNDERGRUUNDis a deliberate misspellingLANGLEYis a metonym of the CIAWWcould be referring to William Webster, DCI (–)- The coordinates 38°57′6.5″N 77°8′44″W point to a spot 53 meters southeast of Kryptos
K3
K3's decryption process is different as it uses a transposition cipher. This means the plaintext characters are already written but in a scrambled fashion.
ENDYAHROHNLSRHEOCPTEOIBIDYSHNAIA
CHTNREYULDSLLSLLNOHSNOSMRWXMNE
TPRNGATIHNRARPESLNNELEBLPIIACAE
WMTWNDITEENRAHCTENEUDRETNHAEOE
TFOLSEDTIWENHAEIOYTEYQHEENCTAYCR
EIFTBRSPAMHHEWENATAMATEGYEERLB
TEEFOASFIOTUETUAEOTOARMAEERTNRTI
BSEDDNIAAHTTMSTEWPIEROAGRIEWFEB
AECTDDHILCEIHSITEGOEAOSDDRYDLORIT
RKLMLEHAGTDHARDPNEOHMGFMFEUHE
ECDMRIPFEIMEHNLSSTTRTVDOHW?I’m actually not quite clear on what was the intended way by Sanborn to solve this. I’ve seen people rearranging the text into grids and applying rotations. The NSA used brute force.
One method is to rearrange the text into a 24-column grid, rotate it clockwise, rearrange the result into an 8-column grid, and then rotate clockwise again:
ENDYAHROHNLSRHEOCPTEOIBI
DYSHNAIACHTNREYULDSLLSLL
NOHSNOSMRWXMNETPRNGATIHN
RARPESLNNELEBLPIIACAEWMT
WNDITEENRAHCTENEUDRETNHA
EOETFOLSEDTIWENHAEIOYTEY
QHEENCTAYCREIFTBRSPAMHHE
WENATAMATEGYEERLBTEEFOAS
FIOTUETUAEOTOARMAEERTNRT
IBSEDDNIAAHTTMSTEWPIEROA
GRIEWFEBAECTDDHILCEIHSIT
EGOEAOSDDRYDLORITRKLMLEH
AGTDHARDPNEOHMGFMFEUHEEC
DMRIPFEIMEHNLSSTTRTVDOHW?
DAEGIFWQEWRNDE
MGGRBIEHONAOYN
RTOISONEEDRHSD
IDEEETAETIPSHY
PHAWDUTNFTENNA
FAOFDEACOESOAH
ERSENTMTLELSIR
IDDBIUAASNNMAO
MPDAAATYERNRCH
ENREAEECDAEWHN
HEYCHOGRTHLXTL
NODTTTYEICEMNS
LHLDTOEIWTBNRR
SMODMAEFEELEEH
SGRHSRRTNNPTYE
TFIITMLBHEIPUO
TMTLEABRAUIRLC
RFRCWETSEDANDP
TEKEPEEPIRCGST
VULIIREAOEAALE
DHMHETFMYTETLO
OELSRNOHTNWISI
HEEIORAHEHMHLB
WCHTATSEYATNLI
DAEGIFWQ
EWRNDEMG
GRBIEHON
AOYNRTOI
SONEEDRH
SDIDEEET
AETIPSHY
PHAWDUTN
FTENNAFA
OFDEACOE
SOAHERSE
NTMTLELS
IRIDDBIU
AASNNMAO
MPDAAATY
ERNRCHEN
REAEECDA
EWHNHEYC
HOGRTHLX
TLNODTTT
YEICEMNS
LHLDTOEI
WTBNRRSM
ODMAEFEE
LEEHSGRH
SRRTNNPT
YETFIITM
LBHEIPUO
TMTLEABR
AUIRLCRF
RCWETSED
ANDPTEKE
PEEPIRCG
STVULIIR
EAOEAALE
DHMHETFM
YTETLOOE
LSRNOHTN
WISIHEEI
ORAHEHMH
LBWCHTAT
SEYATNLI
SLOWLYDESPARATLYSLOWLYTHEREMAINSOFPASSAGED
EBRISTHATENCUMBEREDTHELOWERPARTOFTHEDOORWA
YWASREMOVEDWITHTREMBLINGHANDSIMADEATINYBRE
ACHINTHEUPPERLEFTHANDCORNERANDTHENWIDENING
THEHOLEALITTLEIINSERTEDTHECANDLEANDPEEREDI
NTHEHOTAIRESCAPINGFROMTHECHAMBERCAUSEDTHEF
LAMETOFLICKERBUTPRESENTLYDETAILSOFTHEROOMW
ITHINEMERGEDFROMTHEMISTXCANYOUSEEANYTHINGQ?SLOWLYDESPARATLYSLOWLYTHEREMAINS
OFPASSAGEDEBRISTHATENCUMBEREDT
HELOWERPARTOFTHEDOORWAYWASREMOV
EDWITHTREMBLINGHANDSIMADEATINY
BREACHINTHEUPPERLEFTHANDCORNERAN
DTHENWIDENINGTHEHOLEALITTLEIIN
SERTEDTHECANDLEANDPEEREDINTHEHOT
AIRESCAPINGFROMTHECHAMBERCAUSED
THEFLAMETOFLICKERBUTPRESENTLYDETA
ILSOFTHEROOMWITHINEMERGEDFROM
THEMISTXCANYOUSEEANYTHINGQ?SLOWLY DESPARATLY SLOWLY THE REMAINS OF PASSAGE DEBRIS THAT ENCUMBERED THE LOWER PART OF THE DOORWAY WAS REMOVED
WITH TREMBLING HANDS I MADE A TINY BREACH IN THE UPPER LEFT HAND CORNER AND THEN WIDENING THE HOLE A LITTLE I INSERTED THE CANDLE AND PEERED IN
THE HOT AIR ESCAPING FROM THE CHAMBER CAUSED THE FLAME TO FLICKER BUT PRESENTLY DETAILS OF THE ROOM WITHIN EMERGED FROM THE MIST X
CAN YOU SEE ANYTHING Q ?Notes:
DESPARATLYis a deliberate misspelling- K3 paraphrases Howard Carter’s account of the opening of the tomb of Tutankhamun in which Lord Carnarvon asked Carter if he could see anything
K4
The fourth passage remains unsolved.
---------------------------OBKR
UOXOGHULBSOLIFBBWFLRVQQPRNGKSSO
TWTQSJQSSEKZZWATJKLUDIAWINFBNYP
VTTMZFPKWGDKZXTJCDIGKUHUAUEKCARSanborn provided the following information:
- K1–K3 contain clues to K4
NYPVTT(64–69) decrypts toBERLINMZFPK(70–74) decrypts toCLOCKQQPRNGKSS(26–34) decrypts toNORTHEASTFLRV(22–25) decrypts toEAST
---------------------------OBKR
UOXOGHULBSOLIFBBWEASTNORTHEASTO
TWTQSJQSSEKZZWATJKLUDIAWINFBBER
LINCLOCKWGDKZXTJCDIGKUHUAUEKCARThe solution is being auctioned off with a deadline. In , two journalists found documents in the Smithsonian Archives of American Art that contained the solution to K4.
k5
The solution to K4 supposedly unlocks a fifth passage.
progress
BETWEENSUBTLESHADINGANDTHEABSENC | ABCDEFGHIJKLMNOPQRSTUVWXYZABCD |
SLOWLYDESPARATLYSLOWLYTHEREMAINS | NGHIJLMNQUVWXZKRYPTOSABCDEFGHIJL |
thoughts
Obviously, with the presence of these notes, I’ve taken an interest in trying to crack K4 in my spare time. Here are some thoughts I have:
Kryptos is split into four quadrants:
| k1, k2 | tableau |
| k3, k4 | tableau |
- K1 and K2 in the upper left
- K3 and K4 in the lower left
- tableau in upper right
- continued tableau in the lower right (note the dangling
L) - K1 and K2 both used the same encryption type; K3's was different
- K2 refers to something being buried underground. I’m thinking the lower quadrants (or at least the lower left) represents the underground.
K3 contains the following phrases I find interesting:
The remains of passage debris that encumbered the lower part of the doorway was removed.
The quadrant is somewhat like a doorway, and the remains of passage debris
could be referring to K3's jumbled transposition(?)
With trembling hands, I made a tiny breach in the upper left hand corner and then widening the hole a little, I inserted the candle and peered in.
To me this sounds like an instruction for something to be done with K4. Perhaps K4 is meant to be used to "breach" something in the upper left quadrant.
Also, K4 is shaped like a key. Or maybe a sarcophagus.
Rather than attempting to brute-force a solution out of K4, it might be a better strategy to figure out how every passage is meant to connect and lead to the next.
It’s also possible Sanborn made a mistake somewhere that renders K4 impossible to solve lol.
Work continues in spits and spurts, depending upon time, motivation, and ideas.
— REDACTED
resources
- Elonka Dunin’s Kryptos Page
- A Fresh Perspective on Kryptos K4, the Decades-Old Unsolved Code by
Guillaume Lethuillier